by ZEVAC

Introduction
As aggressive exploration projects around the world uncover new hydrocarbon sources, the demand increases for more pipeline development. However, pipeline operators are under severe financial and social pressure to avoid incidents that cause commodity releases. This means that safe practices must be enforced and that industrial-strength prevention, detection, and mitigation technologies need to be deployed. Regulators are scrutinizing pipeline projects, and the reputation of the industry as a whole is at risk.
“Pipeline integrity” is a term that encompasses a lot of these technologies. It could be argued that in its purest form the term “pipeline integrity” refers to a comprehensive program that ensures hazardous commodities are not inadvertently released from a pipeline and minimizes the impact if a release does occur. Though it is natural to think only in terms of preventing a commodity release, pipeline integrity has a broader definition and comprises three phases:
Prevention activities and solutions seek to avoid commodity releases from occurring in the first place through proper design, construction, operation, maintenance, training, and education.
Detection activities and solutions help pipeline operators quickly identify that a commodity release has occurred.
Mitigation activities and solutions minimize the extent or impact of the released volume and related
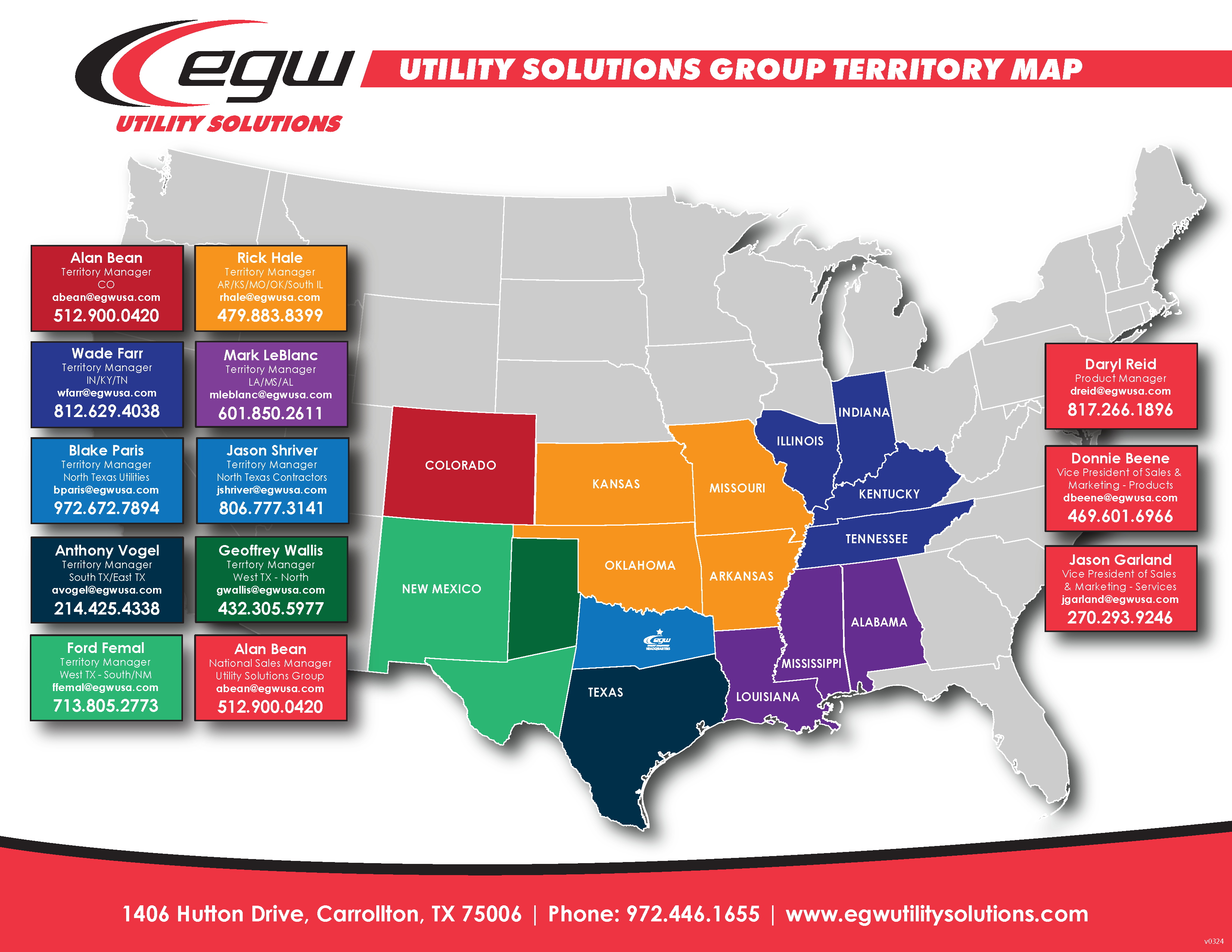
The activities and solutions associated with each of the phases above are distinctly different and have traditionally been looked upon as three separate areas; however, technology and infrastructure have improved over the years, allowing for a more holistic view of pipeline integrity. Some causes of pipeline incidents are under operators’ direct control, others less so, as seen in Figure 1. Pipelines are like all other infrastructure: components and materials degrade over time. Even the most meticulously designed and constructed pipelines must be operated properly and carefully maintained to minimize the risk of a commodity release.
This article reviews in greater detail the different phases of pipeline integrity and gives examples of various factors that affect each phase. Technologies and tools available today to assist pipeline operators associated with each phase are also discussed.
Pigging in Gas Gathering Systems:
Critical Operations
Although not the only aspect of pipeline integrity, preventing commodity releases is obviously of paramount importance. The best defense against a release is to proactively minimize the chances of its occurring in the first place. Technology and tools exist today that help anticipate potential threats to the pipeline and identify anomalies or issues before they become problems. The old adage “an ounce of prevention is worth a pound of cure” holds true for pipeline integrity: the costs associated with avoiding a release are much less than the costs of cleanup, fines, and other civil liabilities — not to mention the damage to a company’s reputation. The process of preventing commodity releases from occurring can be split into the following categories:
• Design & construction
• Operation & maintenance
• Training & education
Design & Construction:
Ensuring pipeline integrity starts with properly siting the route and specifying the technical requirements (e.g., hydraulic calculations, physical properties of piping). Advances in construction practices, such as more sophisticated testing prior to the pipeline’s becoming fully operational, and protective technology further safeguard the pipeline’s structural integrity. The following are some of the more important considerations of pipeline design and construction, along with specific tools and technologies to utilize:
Avoid geo-hazards along the pipeline route
Where the points of supply and delivery are located defines many subsequent engineering design decisions. The geography of terrain along the pipeline corridor may be evaluated with offline design tools such as topographical and geological maps, satellite imagery, aerial photography, and surveys available in the public domain to identify geo-hazards such as landslides, fault lines, soft soils (swamps, bogs), and underground cavities (coal mines, caves).
Ensure that the pump or compressor is sized correctly
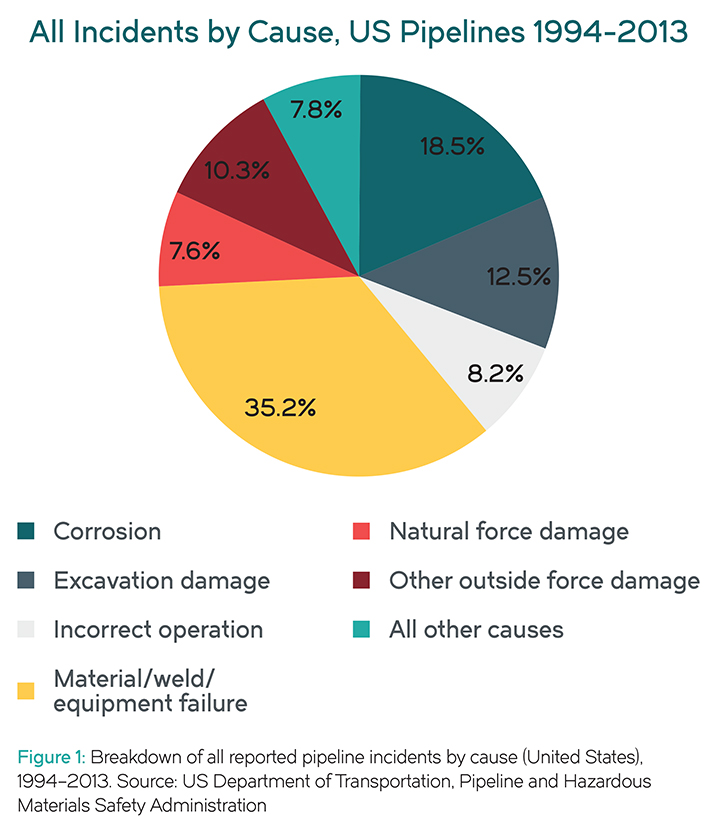
A steady-state pipeline simulation tool can validate the specified size of the pump or compressor through a computational model of the pipeline’s operating conditions (Figure 2). This simulation can also ensure that it is hydraulically feasible for the pipeline as designed to cross the terrain with the selected pump/ compressor setup in an economical fashion.
MarkWest: How They Did It
Ensure that surge suppression equipment is sized correctly
A transient pipeline simulation tool can model the pipeline hydraulics to determine the design criteria for surge suppression equipment. Surge effects like water hammer (a pressure wave caused whenever there is a sudden change in flow, as when a valve at the end of a pipeline closes suddenly) can severely damage a pipeline.
Protect the pipeline against corrosion
Most pipelines are painted with special coatings to limit the chance of external corrosion. Corrosion may be further mitigated with a cathodic protection Cathodic protection controls corrosion of a metal surface by making it the cathode of an electromechanical cell. This is achieved by placing another more easily corroded “sacrificial” metal in contact with the metal to be protected, to act as the anode of the electrochemical cell. For pipelines, where passive galvanic cathodic protection alone is not sufficient, it’s necessary to use an external DC electrical power source to provide sufficient current. This will typically create a situation of overprotection for parts of the pipeline, something that can be avoided by increasing the number of anodes along the pipeline.
Operation & Maintenance
Once the pipeline is in service, continuously monitoring the operational and structural conditions within the pipeline identifies circumstances that, if not mitigated, could lead to a commodity release. Inspection and monitoring technologies provide pipeline operators with the information they need to accurately assess the health of their pipeline and perform proactive maintenance on “at-risk” areas. Some of the more important aspects to monitor and inspect, as well as applicable technologies, include:
Monitor operating pressure
The pressure or head along the pipeline can vary greatly depending on different factors, e.g., elevation. Having a simulation model depict what is occurring within the pipeline in real-time is beneficial. This allows pipeline operators to monitor maximum allowable operating pressures (MAOP) at locations in the pipeline where no physical measurement is available.
Inspect the integrity of the pipeline externally
Advanced non-destructive testing (NDT) methods detect structural damage or degradation in the pipeline from the Ultrasonics or magnetic particle testing are two such NDT methods available in the market today, but there are several others as well. NDT methods uncover anomalies or trouble spots that bear closer inspection by evaluating the integrity of welds and alerting operators to corrosion damage.


Results
Pipeline controllers are in charge of operating some very expensive pipeline assets and should be required to have training or even certification. Training operators on how to recognize situations or conditions that could potentially lead to a commodity release is clearly an important step in prevention. Educating residents living along the pipeline can also help avoid problems. Some considerations to ensure that pipeline operators have the right tools, and other third parties have sufficient information, to prevent a release follow:
Leverage operator training simulators (OTS)
Computer-based simulators for training and evaluation of pipeline controllers are key tools that help improve operational safety and meet regulatory requirements. Enabling the most realistic training experience is essential in making sure the pipeline controller is exposed to both normal operating conditions and abnormal operating conditions.
Follow best practices for human machine interface
(HMI) design Most HMI applications are inadequately designed to allow operators to absorb the vast amount of data and then make good decisions quickly. For guidelines on best practices for HMI design that promote “situational awareness,” albeit within the context of industrial plant operations, see the AVEVA white paper How Human Machine Interface (HMI) Impacts Business Performance in Industrial Sites. More specific guidelines are detailed in the American Petroleum (API) Recommended Practice (RP) publication 1165, “Recommended Practice for Pipeline SCADA Displays.”
Define alarm management hierarchies
Most HMI systems bombard operators with far more alarms than they could ever handle. A well-designed alarm management hierarchy defines different levels of severity, notifying operators only when their intervention is required.
Avoid inadvertent excavation damage
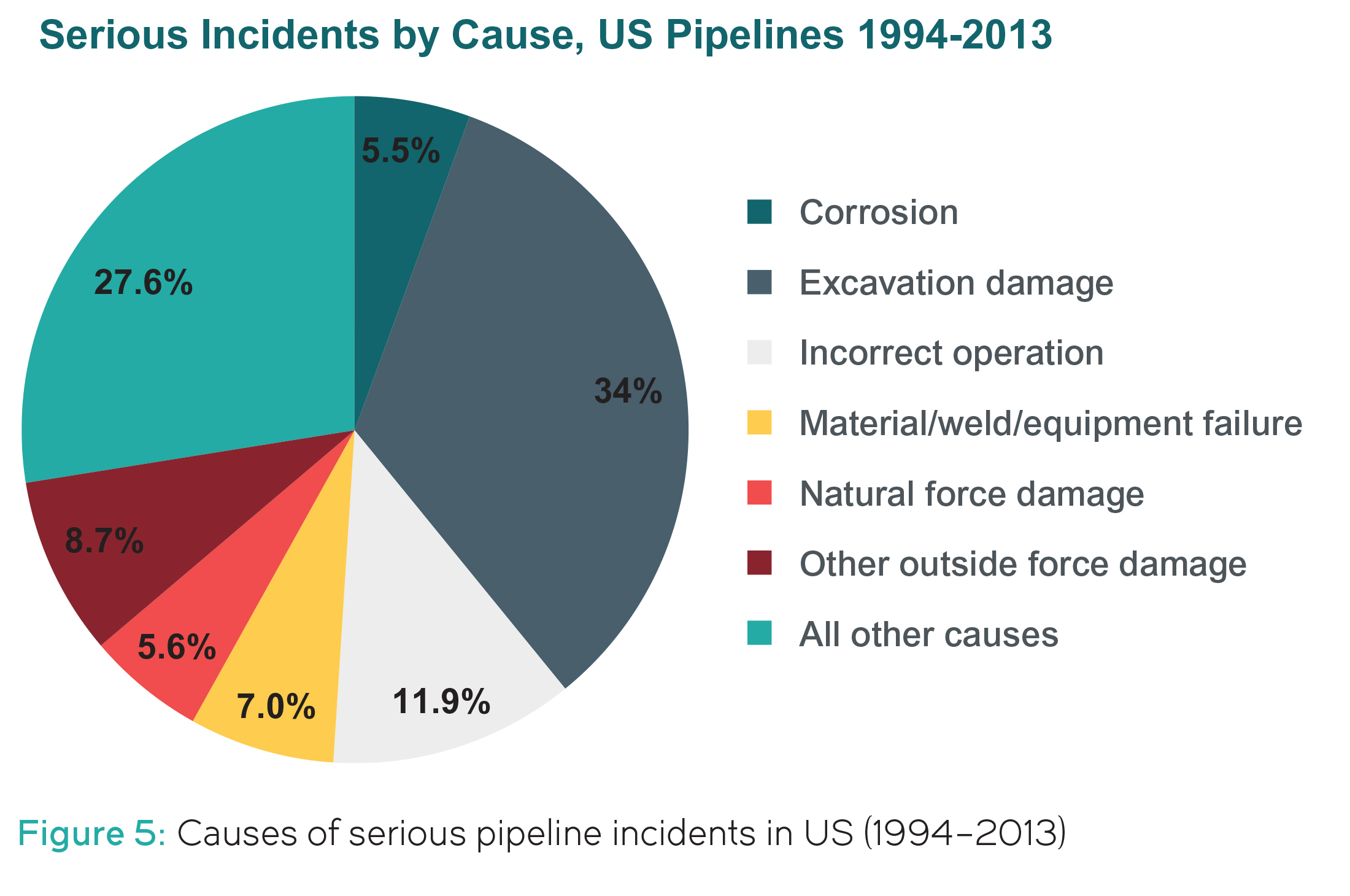
Excavation damage is a leading cause of pipeline incidents — and is a disproportionately larger factor for serious incidents than for all incidents (compare Figure 1 and Figure 5). 1 The pipeline’s right of way should be clearly demarcated with clear and visible signage. A variety of community outreach strategies — flyers, call centers, websites, and “Dig Safe” programs — can educate contractors, developers, municipal works departments, and the general public about how to avoid inadvertent damage to the pipeline.
Pigging for Pipeline Integrity
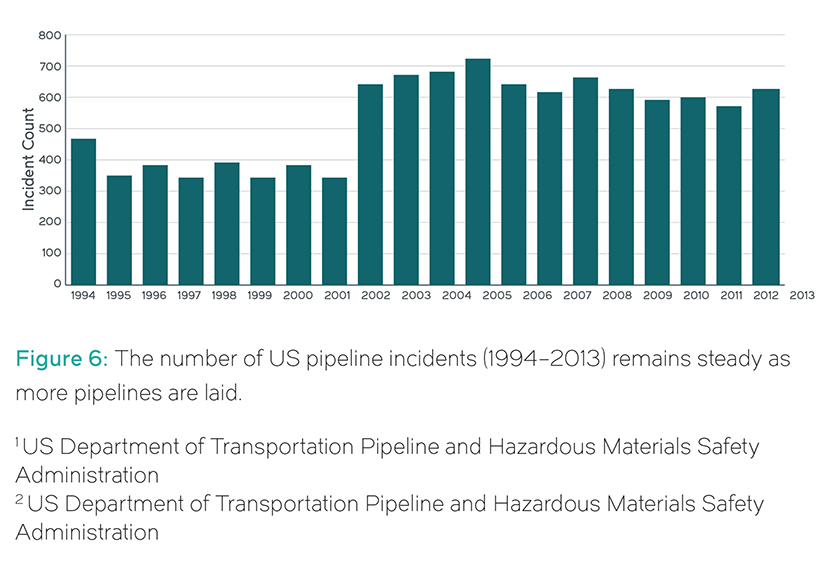
Although moving commodities via pipeline remains the safest means of transport, even the best-constructed and –operated pipelines are at risk of a commodity release. In the United States alone over the past decade, more than 10,600 incidents were reported, with property damage totaling over $6 billion (€4.75 billion). Even with advances in detection technology, the number of incidents has not decreased significantly as more pipelines are laid (Figure 6). 2 Commodity releases incur liabilities for pipeline operators, with major liabilities usually related to serious incidents where the reliability of the detection system was in question. The ability to notice small changes that could indicate a release and, if a release has indeed occurred, localize the problem or shut down the pipeline quickly is a key component of pipeline
integrity.
The tools and technologies for detecting commodity releases after they have occurred can in essence be split into two categories:
• External-based systems
• Internal-based systems, also called computational pipeline monitoring (CPM)
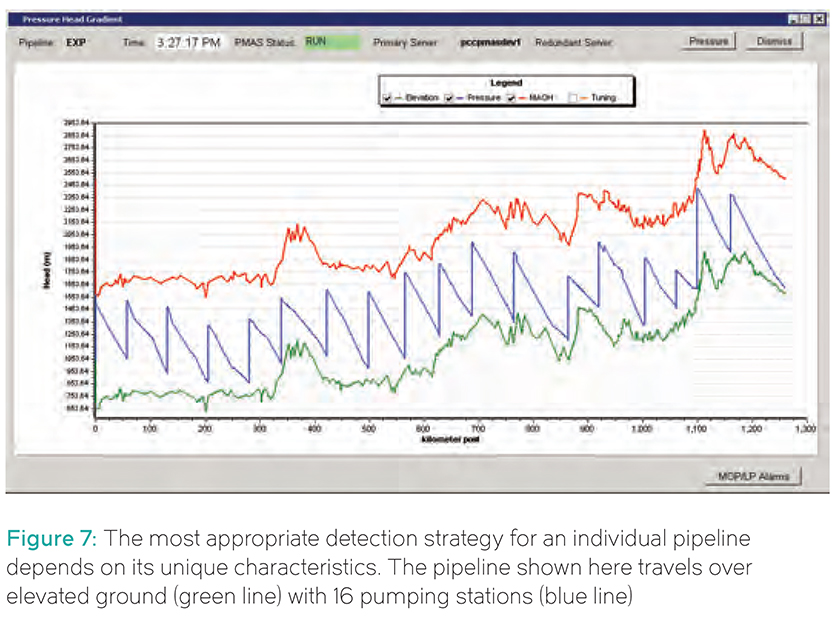
A pipeline operator could have one or both of these types of detection systems installed on the same pipeline. Each pipeline is unique, and the specific methodologies used for one pipeline might not be useful for another. For example, the hydraulic profile below (Figure 7) displays a pipeline that is more than 1,100km (683 miles) long. A pipeline of this length would require different types of detection compared with a pipeline that is only 4km (2 mi.) long. The hydraulic display also shows the head profile for this pipeline (the blue saw-like line), which indicates that this pipeline has at least 16 pump stations and goes over terrain that is gradually increasing in elevation, as seen by the green line at the bottom. A pipeline that goes downhill or over flat terrain would potentially require a different detection methodology.
“Each pipeline is unique, and the specific methodologies used for one pipeline might not be useful for another.”
“No two pipelines are the same, and each needs to be analyzed individually.”
Dominion Energy: How They Did It
The red line at the top indicates the maximum allowable operating head (MAOH) for this pipeline. The MAOH for a pipeline constructed with different materials would be different from this one, and a different detection methodology might be more appropriate. Notice also that the slope of the blue line occasionally changes, which indicates that this pipeline probably transports multiple products or that the diameter of the pipeline is different in places. All these factors affect which type of detection system operators would choose for their pipeline. No two pipelines are the same, and each needs to be analyzed individually.
External-based pipeline detection
External-based pipeline commodity release detection has been around since pipelines were initially used to transport any type of fluid. It essentially involves looking at the external surroundings and detecting the release on the outside of the pipeline wall.
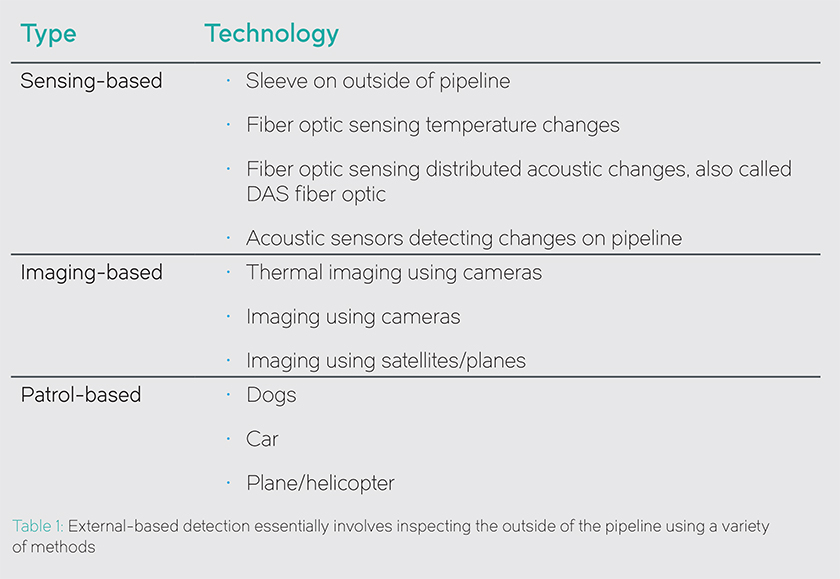
External-based detection systems are increasingly employed because of their ability to detect very small spills and locate commodity releases with a high degree of accuracy. Table 1 summarises the technologies associated with external detection:
Unfortunately, while external technologies can be retrofitted to existing pipelines, the fieldwork to do so is still relatively expensive, especially so for longer pipelines. However, new and shorter pipelines are increasingly using external technologies to complement internal-based or CPM- based commodity release detection applications.


These five CPM methods can be classified according to two different alarming principles underpinning their detection algorithm:
Conservation of mass methods work on the principle that whatever enters the pipeline must be equal to whatever exits the pipeline, adjusted for change in inventory of the pipeline. The line balance CPM, real-time transient model CPM, and statistical analysis CPM techniques can base detection on this method.
Signature recognition methods consider the relationship of system pressures and/or flows, or recognize anomalies in sensor outputs on the pipeline. The real-time transient model CPM, statistical analysis CPM, pressure/flow monitoring CPM, and the acoustic/negative pressure wave CPM techniques can base detection on this method.
General considerations for evaluating CPM systems
No one single commodity release detection system is optimal for the entire range of pipelines operating in widely diverse environments. Different pipelines call for different types of commodity release detection systems. Therefore, a comprehensive analysis is necessary to identify which CPM technologies and methods are best suited for the particular pipeline. A simple A-to-B pipeline route might have simpler operations than a pipeline with many active route connections and elevation changes, multiple receipts and delivery points, and reversible flow. The more complex the pipeline, the more flexible the CPM needs to be to handle all possible operational scenarios.
The following list of key factors to consider when evaluating a new CPM (or re-evaluating a legacy system) for its detection capability should be weighted according to their importance to any particular operation:
• Rate of false alarms and misses
• Sensitivity to pipeline flow conditions such as transients, shut-ins, starts, and stops
• The impact of instrument accuracy and configuration accuracy
• Personnel training and qualification requirements
• Required response time
• Accuracy and precision in estimating location and volume of release
• Ability to detect pre-existing releases
• Robustness/high availability
• Initial cost/tuning costs/maintenance costs
The most important goal in selecting a commodity release detection system is the ability to identify a commodity release quickly enough to mitigate the safety and environmental risk while also meeting the operator’s overall business objective. This includes the potential value of product lost, the cost of clean- up and potential regulatory fines, potential detriment to surrounding environments, and the cost to reputation and potential impact on future projects.
“When selecting a commodity release detection system, it is important to evaluate each pipeline independently.”
Conclusion
All pipeline companies in the world have as their primary goal and concern that the transportation of commodities be safe and reliable. Regulators, operators, and vendors need to continue to invest heavily in detection and mitigation tools and best practices, as commodity releases will continue to happen no matter how strong the prevention measures.
Taking a holistic approach to commodity releases and not looking upon prevention, detection, and mitigation as independent and separate aspects of pipeline integrity benefits the pipeline company, the public in general, and the environment.
Additionally, it is important to realize that there is no optimal “one size fits all” commodity release detection system for all pipelines in every environment. Each pipeline is unique and requires an individual evaluation. Pipeline operators need to weigh business objectives against their threshold for risk. At the intersection of those points is where companies will find the appropriate commodity release detection system solution.
For instance, a sophisticated commodity release detection system may be justifiable for a pipeline in a highly-populated area, but impractical in another environment. Different CPM methodologies and external commodity release techniques provide potentially complementary commodity release detection capabilities, so different methods, or a combination of methods (tiered approach), might be the right fit overall.
For more information on the ZEVAC and to request a demonstration, click here.
Download a PDF version of the White Paper here.
About ZEVAC
ZEVAC was founded in 2014 as TPE Midstream and holds multiple issued and pending patents on the ZEVAC and its underlying technology. ZEVAC also operates a full-service equipment rental division, with offices in Pittsburgh PA, Tulsa OK, and Temecula CA. ZEVAC supports operators by providing the equipment they need to perform pipeline system maintenance safely while being heroes in their neighborhoods and taking care of the environment they operate in.